
Post by : Anis Al-Rashid
In the past, crafting a “strong password” felt sufficient for online security, combining numbers, symbols, and upper-case letters. However, that confidence is now unwarranted.
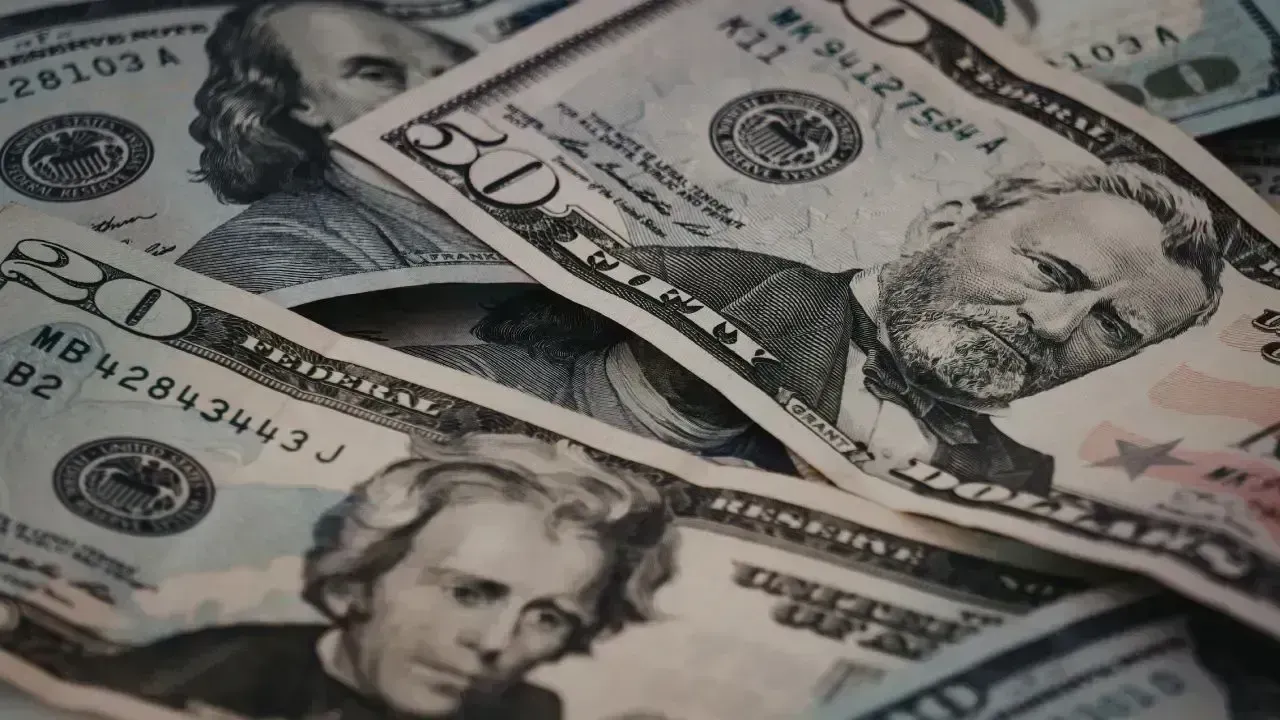
Data breaches are frequent, and password leaks happen as exposed databases circulate. Phishing attempts mimic legitimate sources, while malware silently captures keystrokes. Once a password is compromised, it can rapidly spread through underground networks. Hackers have shifted from guessing passwords to purchasing them.
The key question has evolved from “Is my password strong enough?” to “How soon will my password be compromised?”
And for many, the answer is unsettling.
Two-factor authentication (2FA) introduces an additional layer of security, providing a second verification point for accessing your account. Even if someone obtains your password, they still need another factor under your control—typically your phone, a fingerprint, or a one-time code.
Instead of relying on a single key, your account demands two distinct proofs of identity.
Examples of this second check include:
A time-sensitive one-time code
Approval via push notification
Biometric verification like a fingerprint or facial recognition
A hardware security key
A backup code mechanism
This process transforms a simple lock into a double gateway.
Hackers tend to steer clear of accounts that employ 2FA because it disrupts automated attacks.
A majority of modern hacking is conducted automatically, with scripts trying millions of passwords across numerous platforms. When a live mobile code is required for an account, an automated attack collapses. Machines can’t receive texts or approve login requests.
While two-factor authentication isn’t foolproof,
it significantly slows down criminal activity.
Most cyberattacks don’t start with bank accounts. Instead, they target the most vulnerable areas.
Examples include:
Once compromised, attackers reset passwords on various websites through email access, with a single weak account serving as a master key to a user’s entire online presence.
People don’t lose data outright.
Access is what’s truly lost.
Malware makes noise.
Data leaks, however, are quiet.
Once your credentials are leaked:
Hackers don’t rush.
They bide their time.
They slowly test accounts.
They analyze user behavior.
Even a year after a breach, accounts may remain vulnerable as many individuals neglect to update their passwords.
However, implementing two-factor authentication offers protection.
Leaked passwords become much less dangerous.
It’s common to think that only banks require protection.
That misconception is damaging.
An account with an online retailer discloses your home address.
A delivery service reveals your daily habits.
A social media account sheds light on your relationships.
An email account governs identity resets.
A cloud storage service holds sensitive documents.
Hackers are no longer focused solely on bank accounts.
They pursue identity theft.
And that identity comes from seemingly benign apps.
Many avoid two-factor authentication due to perceived inconvenience, not because it’s hard.
That extra verification step can feel tedious when:
Yet, inconvenience is precisely what deter criminals.
If security feels effortlessly smooth, it’s likely inadequate.
Protection that is a bit uncomfortable often proves to be the most effective.
Victims of cyberattacks often express:
“I never thought it would happen to me.”
Many assume they are too insignificant to attract attention, too ordinary to target, or too unknown to be of interest.
Hackers are indifferent to who you are.
They care only about what they can access.
Automation in attacks knows no discrimination.
When an account is compromised:
Photos may disappear.
Funds may vanish.
Friends may be deceived.
Reputation may suffer.
Data may be lost.
And recovery can be a lengthy process.
Or worse, sometimes impossible.
Implementing two-factor authentication safeguards not just accounts.
It protects cherished memories.
While text-message verification enhances security beyond just passwords, it’s not without flaws.
Attackers can hijack phone numbers through methods like SIM swapping.
More secure options include:
App-based authentication
Physical security keys
Device-level security checks
The stronger the second factor, the higher your account's security level.
When enabling two-factor authentication, many neglect to save backup codes, which is a risky oversight.
If you misplace your phone and lack backups, you could become permanently locked out.
Practicing safe habits includes:
Printing backup codes
Storing them offline
Maintaining multiple copies
Using secure storage options
Security measures without recovery options can lead to dire situations.
A common misconception is that advanced security measures are exclusive to tech-savvy individuals.
This is incorrect.
Digital safety has become as essential as locking the front door.
There’s no need for technical expertise—just a willingness to protect oneself.
While monetary losses may be recoverable, trust often is not.
When accounts are hijacked, victims frequently experience feelings of violation, shame, helplessness, anxiety, and exposure.
Many don’t understand that being hacked feels remarkably personal.
Because it truly is.
Your digital identity is intertwined with who you are in the real world.
Just as you lock your doors at night, your accounts deserve similar safeguards.
Implementing two-factor authentication should extend to:
Email accounts
Bank applications
Payment services
Social media platforms
Cloud storage accounts
E-commerce sites
Workplace systems
Security should not be discretionary.
It should be a habit.
Without robust authentication, we can expect:
An increase in identity theft
A rise in online fraud
A decline in digital trust
A loss of privacy
A decrease in financial confidence
The digital landscape will feel threatening.
Unless we evolve.
With strong authentication measures in place:
Fraud becomes more challenging
Privacy is fortified
Access is more secure
Trust is restored
Confidence is regained
Even simple changes can yield substantial protective benefits.
Two-factor authentication is no longer just advisable.
It’s imperative.
Not due to an expectation of danger,
But because the threat anticipates you.
Each login serves as a portal.
And every portal requires vigilance.
The secondary verification step is the ultimate hurdle.
Employ it.
DISCLAIMER
This content serves informational purposes only and does not provide technical or cybersecurity recommendations. Readers should consult qualified experts for personalized digital security advice.





WhatsApp Experiencing Issues Today? Global Users Report Delays
WhatsApp users around the globe are facing message delays and issues. Discover the reason behind tod

Is Your Android Monitoring You? Disable These 6 Settings Immediately
Concerned about your Android's monitoring? Discover 6 essential settings to change now for better pr
Boost Your Health with These 7 Protein-Packed Indian Foods
Explore 7 protein-rich Indian foods that can enhance your daily nutrition naturally and affordably.

Comprehensive Breakdown of Family Living Costs in Dubai: Monthly Expenses, Rent, and Education
Explore what a small family can expect to spend in Dubai monthly, covering rent, schools, groceries,

Top High-Income Skills You Can Learn at Home
Discover high-income skills such as writing and digital marketing that can boost your earnings while

The Hidden Impacts of Daily Breakfast Skipping on Your Body
Learn how skipping breakfast can significantly impact your energy, mood, and overall health in every