Post by : Anis Al-Rashid
Digital identity is facing mounting pressures from the dual challenges of expanding services and increasing risks. The proliferation of services, users, and devices has led to an explosion of identity interactions. Meanwhile, identity systems are constantly under threat from phishing, credential theft, and other sophisticated attacks. Traditional username-password setups are becoming outdated.
Companies are now examining whether they can transition to a system that is passwordless (eliminating the need for users to remember credentials), private (safeguarding users' identities from unnecessary exposure), and secure (thwarting attacks before they occur). These three principles—passwordless, private, secure—are prominently featured in vendor marketing but are challenging to achieve simultaneously.
Passwordless identity refrains from using a “something you know” secret (password) and replaces it with “something you have” (like a device or token) or “something you are” (such as biometrics). This shift away from secrets mitigates many familiar vulnerabilities. pingidentity.com+2Microsoft Learn+2
Privacy in identity management emphasizes the minimization of unnecessary data storage and sharing. It allows users to control which attributes they share and with whom. Keyless+1
An effective security model means resisting known threats like credential stuffing and phishing attacks while maintaining standards of encryption, auditability, and resilience. RSA
While each goal is crucial, the real complexity lies in integrating an identity solution that accomplishes all three at once.
Standards such as WebAuthn and FIDO2 are moving toward cryptographic keys tied to devices, enhancing phishing resistance since no passwords are stored on servers. Organisations implementing these strategies report lower demands on help desks and reduced attack vulnerabilities. FIDO Alliance+2Microsoft Learn+2
Current systems are centralized, but emerging self-sovereign identity (SSI) models allow users direct control over their attributes, sharing only what's necessary while verifying without excessive data exposure. Research in decentralized biometrics is on the rise. arXiv+1
More platforms are endorsing biometric authentication that keeps data on the device to enhance security. Solutions are being offered where biometric data is neither stored nor reconstructed. Keyless
Identity-as-a-Service options now support passwordless operations, device binding, and consent-based data sharing. These offerings assist in transitioning away from outdated credential systems to more secure digital identities. 1Kosmos+1
Due to increased scrutiny in identity and data security (like GDPR), enterprises are compelled to select secure, privacy-focused solutions, prompting vendor innovation.
Eliminating passwords diminishes many common attacks. Companies employing passkeys report significantly fewer theft incidents. pingidentity.com+1
By doing away with password management, user convenience increases, resulting in improved engagement and swifter log-in experiences. FIDO Alliance+1
Costs associated with help-desk support for password issues can be substantial. Adopting passwordless solutions can greatly reduce these expenses. pingidentity.com
Moving verification to user-controlled devices minimizes privacy risks, improving trust and compliance efforts.
Organisations adopting cutting-edge identity solutions are better equipped for changing threats and upcoming regulatory frameworks.
A significant challenge is device-bound credentials: losing a device complicates access. Hence, it’s vital to establish secure recovery methods. TechRadar
Many businesses still rely on traditional identity options, making the shift to a passwordless model complicated due to system compatibility and change management requirements.
While users favor convenience, they may overlook the implications of biometric data use, necessitating thorough audits of vendor claims.
Even without passwords, identity systems are still vulnerable to various attacks, requiring robust security architecture that captures new vulnerabilities.
Despite the existence of standards like FIDO2, real-world support varies widely, which can undermine user experience and security.
An identity system can falter if users are improperly integrated or supported, making user education crucial.
Identify areas of highest identity risk and weigh the financial impact of identity-related failures to direct modern solution deployment.
Create a comprehensive map of your identity landscape, including existing credential methods, access flows, and legacy system integration plans.
Choose solutions aligned with open standards and robust security measures, ensuring a privacy-preserving approach with minimized data disclosure.
Design effective recovery procedures to secure user accounts without compromising privacy. Develop a lifecycle management strategy for devices.
Constantly track data on login success rates, phishing incidents, and user satisfaction to guide the adoption of new identity solutions.
Communication about the new identity management processes and their benefits will be key to successful user adoption.
Incorporate upcoming trends like zero-trust identity systems and quantum-resistant algorithms into your strategic planning.
Major providers are moving towards using passkeys as default for new accounts, indicating a significant evolution in identity systems. The Verge
Models permitting user-controlled credentials based on blockchain technologies will see greater adoption and proof-of-concept implementations. arXiv
Biometric verification will increasingly occur on-device, alleviating privacy concerns significantly in sensitive sectors like healthcare. Keyless
Identity infrastructures will increasingly align with zero-trust principles, where identity serves as the core trust measure.
Stricter regulations surrounding identity and sensitive data highlight the need for strong privacy measures, offering a competitive edge to compliant solutions.
As quantum computing evolves, identity systems will need to adopt standards that safeguard against quantum threats, especially for long-term credentials. arXiv
The vision of digital identity solutions that are passwordless, private, and secure is becoming a reality with many organizations making headway. The transition towards cryptographic credentials, user-managed identity, and privacy-centric biometrics is underway.
Nevertheless, these ideals are not without challenges. Legacy systems, recovery mechanisms, and user behavior all play crucial roles in maintaining security beyond simply forgoing passwords. Successful identity initiatives will recognize identity as a strategic advantage and foster ecosystems where passwords diminish, user privacy is enhanced, and security risks are diminished.






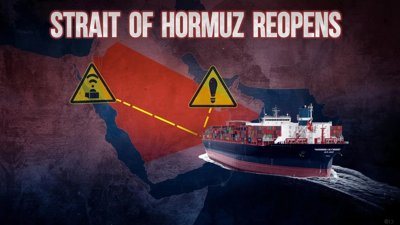
Iran Reopens the Strait of Hormuz Under New Regulations
Iran's reopening of the Strait of Hormuz comes with new rules that could affect global shipping and
Understanding Akshaya Tritiya 2026: Key Dates, Rituals, and Gold Purchase Insights
Explore the significance, date, and best practices for buying gold on Akshaya Tritiya 2026.

Top 10 Experiences for First-Time Visitors to NYC
Uncover 10 must-do activities for first-time NYC visitors, including iconic sights, local flavors, a

7 Everyday Practices for Natural Belly Fat Loss
Explore 7 everyday habits that help in burning belly fat naturally without drastic dieting. Simple s

The Compounding Effect: Transforming $5,000 into $120,000 Over Time
Learn how compounding can evolve a $5,000 investment into $120,000 through time and the right strate

Blood Sugar Testing: Morning vs After Breakfast – What You Need to Know
Explore when to check your blood sugar: fasting or post-breakfast for better health insights.